Insights
Real experiences and insights that shape outcomes

Whether you are a bank or financial institution that handles sensitive information, odds are that you face various threats to compliance, privacy, and many similar areas. With the introduction of new technologies, here we will look at emerging digital risks and compliance issues in the areas of existing IT systems, cross-enterprise integration, process impact, and blockchain adoption, and also discuss tools that can provide new insights, such as graph information and new security analytics.
The key digital initiatives in the banking, financial services, and insurance (BFSI) sector for 2023 include an online platform called the Cyber Risk Matrix. An organization’s risk management function necessity a detailed understanding of the frequently developing risks as well as the practical tools & techniques accessible to address them. Cyber risk is a risk related to “financial loss, disruption or damage to the reputation of an establishment from some kind of disappointment of its information technology structures”. The same matrix may be considered by all companies and the specific areas may be focused on.
As big businesses carry on accepting cloud infrastructure & approaches, the urgency for IT to implement cyber risk management measures to tackle cybersecurity risks is high. Though new technologies bring productivity gains, at times, this can be at the cost of data security. This present situation demands an integrated cyber risk management method for undertaking all cybersecurity risks & threats in cyberspace.
Multiple security technologies are leveraged through Cyber risk management platforms such as SIEM, advanced & next-generation networks, endpoint security & DLP, provided that deeper analytics & insights for an integrated method to grip the overall threat lifecycle & address cybersecurity risks holistically.
A cyber risk matrix is a tool that helps organizations assess and prioritize their cyber risks based on the impact and likelihood of different scenarios.
Inter-company integration is the process of combining or aligning the operations, systems, and culture of different entities within the same group or organization. It can involve various aspects such as finance, accounting, human resources, IT, sales, marketing, etc. Some of these are,
Integration risks may not mean just IT-related or system-wise integration issues that may appear when one changes some kind of system support for an operational scenario. Let’s list them all and take a look at the possible mitigation strategies for each one.
IT systems are a vital piece of operations and it’s impossible to conceptualize an operational landscape without such support. Changing something at the operations level that prompts current systems or entering systems to integrate in a different way or with different systems to bring about change itself is a serious risk. To mitigate this issue, one needs to:
People tend to resist change, moreover, if that change entails responsibility increase, service level improvement, cycle team reduction, or activity proliferation. To mitigate this, we need to seriously engage in managing the impacts of putting people in the line. Some of the key considerations are:
Changing a process, for whatever reason, means that one will do either new things or change the way it is already being done. Either way, there are critical integration aspects at the process level that one needs to focus on:
Applying these strategies when changing an operation ensures that we eliminate integration risks. Everyone involved can approach change with confidence.
Graph information in risk and compliance can help organizations to:
There are general risks associated with blockchain development such as underdeveloped standards, high energy demand, data privacy, and legislation. Other risks include trusting blockchain managers & developers, transaction speed, and malicious users. Apart from this, there are legal risks that are more severe. Enforce the laws to protect the users while implementing blockchain technology. Governments are also keen to govern the new technology centrally. Government makes these rules to protect the interests of the user and the service provider.
Data privacy is the biggest concern when it comes to distributed ledger technology. By nature, different geographies store a copy of this data. It means that it can easily fall under a massive multitude of jurisdictions — making data privacy a very complex subject.
The GDPR regulation is aimed explicitly at EU citizens. Another thing that makes data privacy complex is the fact that the data is immutable on the blockchain. No user, in any case, can remove the information once stored from the blockchain database.
The jurisdiction and dispute resolution are big concerns. A distributed ledger is all about a decentralized network, which makes applying jurisdiction an inevitable problem. Smart contracts can help to program avoid violation of jurisdiction, but the challenge is to enforce the use of jurisdiction. The process of dispute resolution is challenging and needs resolution. Overall, it is tough to resolve the issues considering the nature of the DLT.
The last blockchain legal risk is a regulatory risk. Governments have to pass regulations to the DLT. In some cases, states are also empowered to make their own regulations, which can make things more complicated. With the rise of digital currencies, it is common to have federal regulations so that they can protect the interest of the users and keep the economy in balance. There are also security risks associated with blockchain.
The decentralized blockchain has to interact with humans in order to work correctly. In that case, new blockchain security risks come in. Hackers can steal credentials when a user is interacting with the computer. It only happens at endpoints, which makes blockchain vulnerable.
The whole idea of blockchain or distributed ledger technology relies heavily on public and private keys. Hackers try to obtain the keys by attacking the weakest point as they are difficult to guess. It can be a mobile device or a personal computer.
Many ad-hoc platforms and services work with DLTs to improve their functionality. Scan the 3rd party vendor platforms for vulnerability to avoid issues during the run-time. The security risks can come due to bad code, weak security, and wrong handling by the persons. Vendors must ensure that smart contracts are free from all kinds of flaws or security loopholes. If there is one, then it can easily lead to a system-wide effect.
The quality of the code remains a big concern to most blockchain solutions. Decentralized organizations need to take extra care when they deploy their solutions. One such example is the Decentralized Autonomous Organization (DAO). It is an autonomous system that automates a certain or the whole organization.
Run the DLTs on a small scale before going live. To test the DLT, the developers need to use “testnet” which simulates the network. They can do a wide range of tests. However, it doesn’t cover the issues that can come at full scale.
As an organization, you need to understand that risk and compliance play an important role in securing data and governance as you execute digital transformation initiatives. Alongside the IT transformation, people and processes are equally important to establish safeguards during inter-company integrations.
Grep Digital helps businesses to adopt the best technology practices to maximize their return on investments. Connect with us to partner in your digital transformation journey.

Introduction In the software industry, product incubation is an essential aspect of innovation and growth. The Build-Operate-Transfer model (BOT) is a cost-effective and flexible
Read moreIntroduction Conversational bot is one of the most exciting applications of NLP is the development of interactive and intelligent bots. These bots have the poten
Read more
Availability of talent can be a major challenge for businesses of all sizes, as it can limit growth and hinder the ability to take on new projects and opportunities. While it can b
Read more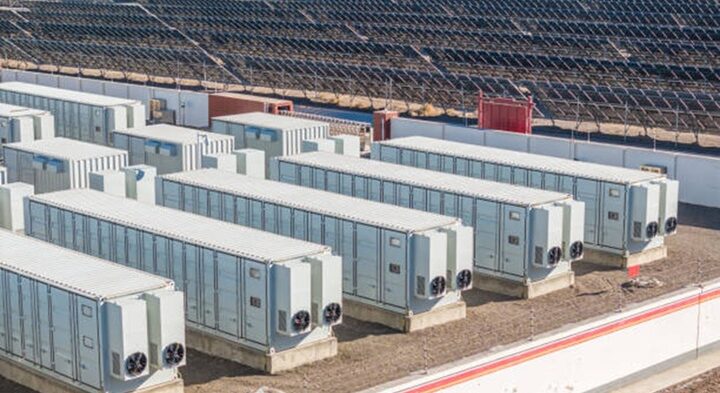
Modern solar energy environments continue to grow in complexity. Solar generation, grid supply, battery storage, and generator backup now operate as a single interconnected system.
Read more
Introduction Data Management Solutions play and important role in meeting the net zero targets. In the global quest to combat climate change, green energy utility providers play a
Read more Technogrep Solutions LLP
HD-022, WeWork Pavilion,
62/63 The Pavilion Church Street,
MG Road, Bangalore,
India-560001
✉ info @ grepdigital.com